Note: I’ve previously written on how to setup your own home VPN using a Linux machine and PiVPN. This new approach does not require setting up port-forwarding and/or the transportation of keys to connecting machines.
A new collection of Software Defined WANs are now more well developed than ever and while SDWANs have been fairly common place in commercial settings their usage in personal networking has been limited. Two providers which have changed this since 2020 are: (a) TailScale and (b) ZeroTier – amongst others. You may ask a good question at this point – why would I use a SDWAN?
In this post I’ll try to introduce SDWANs, but we’ll also look at the steps to set it up. SDWANs like TailScale now offer a way to set up a logical network which might be distributed and split over multiple other LANs and WANs. Machines can be logically grouped together and securely connected to one another without a need to configure routers or modify address tables and packet routing. If this is sounds awesome – its because it is.
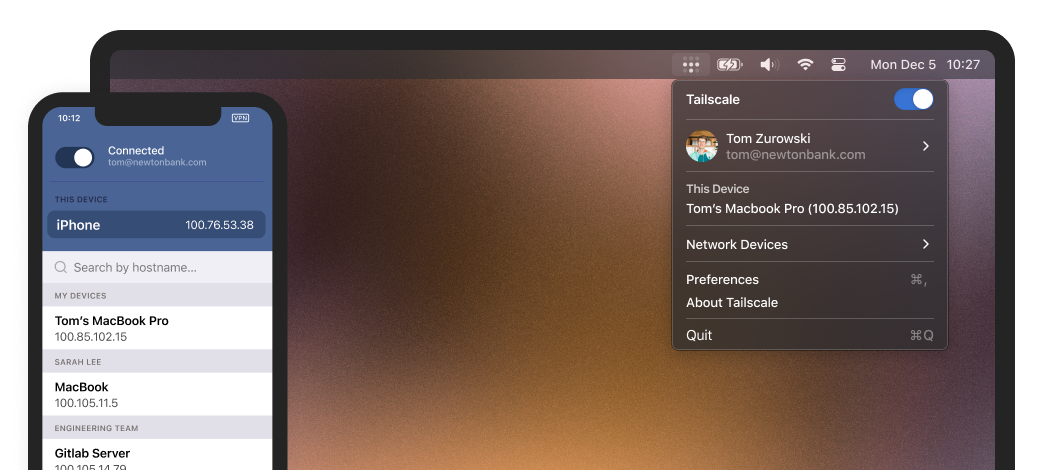
For several years my home VPN has worked on PiVPN and the manual mechanisms of port-forwarding and setup can be bewildering to novices or those wanting to quickly setup a secure network. SDWANs make such a setup largely effortless. The SDWAN peer software needs to simply be installed on each machine which is to be included. A machine can be included on several SDWANs and each SDWAN operates through a separate network interface (e.g. tailscale0 etc).
TailScale will traverse multiple NATs for instance, you might have multiple machines/peers connected to mobile phone network data. Their IPs may change periodically. TailScale translates through the complexity via the Overlay network and you can happily communicate with those peers as they flip and change their WAN IPs. If you’re into IoT related network creation, where peers are split geographically, then TailScale and ZeroTier may be extremely valuable to you.
In the remainder of this post, I won’t go into the details of how SDWANs work, but I’ll give some basics on how to install Tailscale, but also setup so-called ‘Exit Nodes’ which act much like a network endpoint – which act as a VPN server in one or more remote locations.
Setting up Tailscale requires you download the respective client/peer software for your device. For this example I’m going to focus on the Raspberry Pi. The process is straightforward on typical operating systems like Windows, MacOS and Ubuntu Desktop. As a first stage you’ll need to create a Tailscale Account which can be done here.
Visit the Download Tailscale Webpage: https://tailscale.com/download to see several instructions for several platforms.
If you’re setting up your Raspberry Pi with Ubuntu Linux the following commands can be used.
#Add Tailscale’s package signing key and repository
curl -fsSL https://pkgs.tailscale.com/stable/ubuntu/focal.gpg | sudo apt-key add -
curl -fsSL https://pkgs.tailscale.com/stable/ubuntu/focal.list | sudo tee /etc/apt/sources.list.d/tailscale.list
#Install Tailscale
sudo apt-get update
sudo apt-get install tailscale
#Authenticate and connect your machine to your Tailscale network
sudo tailscale up
# View Tailscale address
tailscale ip -4Tailscale creates a separate Virtual Network Interface which data traffic can flow over for communication between peers. To setup your Raspberry Pi or other computer as a VPN ‘Exit Node’ which means that the node will act as a proxy for Internet traffic – then we need to do a few other basic operations which are well detailed on the Tailscale site.
Tailscale
The exit node feature lets you route all non-Tailscale internet traffic through a specific device on your network. The device routing your traffic is called an “exit node.”
By default, Tailscale acts as an overlay network: it only routes traffic between devices running Tailscale, but doesn’t touch your public internet traffic, such as when you visit Google or Twitter. This is ideal for most people, who need secure communication between sensitive devices (company servers, home computers), but don’t need extra layers of encryption or latency for their public internet connection. However, there may be times when you do want Tailscale to route your public internet traffic: in a cafe with untrusted Wi-Fi, or when traveling overseas and needing access to an online service (such as banking) only available in your home country.
From the node that we want to run as an exit node, we need to run the tailscale service statup with an advertisement that it may be used. To do this we execute the following command. The –accept-dns=false is used for routing through a specified DNS, in this case you may have one of your nodes running PiHole, but you could also redirect DNS traffic through a set of public DNS nameservers (e.g. 1.1.1.1, 1.0.0.1).
sudo tailscale up --advertise-exit-node --accept-dns=falseThe node should now show up as a potential exit node. The next stage is to modify the routing on your Tailscale Web Dashboard to allow other peers/nodes to use it.


That should be the process completed. You can force the usage of the Exit Node via a command-line or you can specify the usage of the exit node via your Tailscale App. Further details on using TailScale with PiHole can be found here.
Happy Interwebbing.
