While paid for VPN (Virtual Private Network) systems and subscriptions exist, a great and low cost means by which to access your own home or work network is to use a VPN setup using Ubuntu (any PC with Ubuntu) or Raspberian OS (Raspberry Pi) in combination with PiVPN.

PiVPN is an awesome packaged installation of libraries and tools including OpenVPN. It’s makes it extremely quick and easy to install and setup a VPN server.
Added official details may be found here: https://github.com/pivpn/pivpn/blob/master/README.md
To install PiVPN execute the command as root from a terminal:
curl -L https://install.pivpn.io | bash
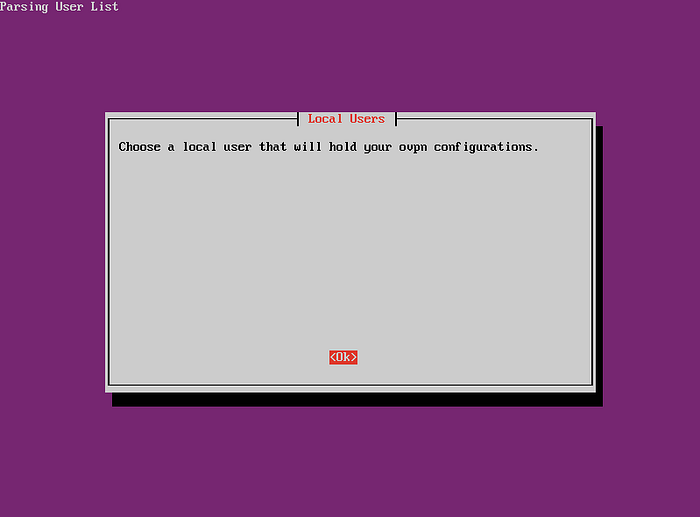
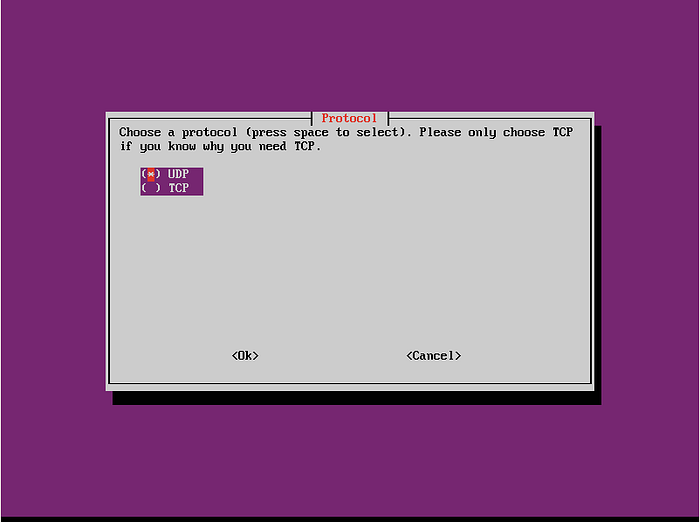
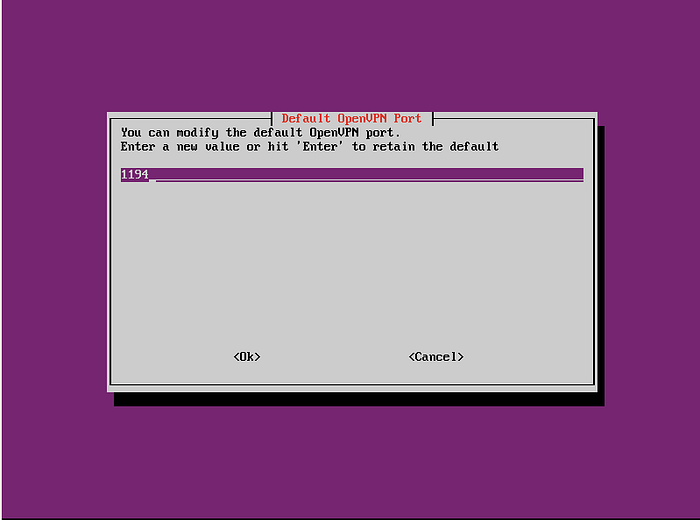
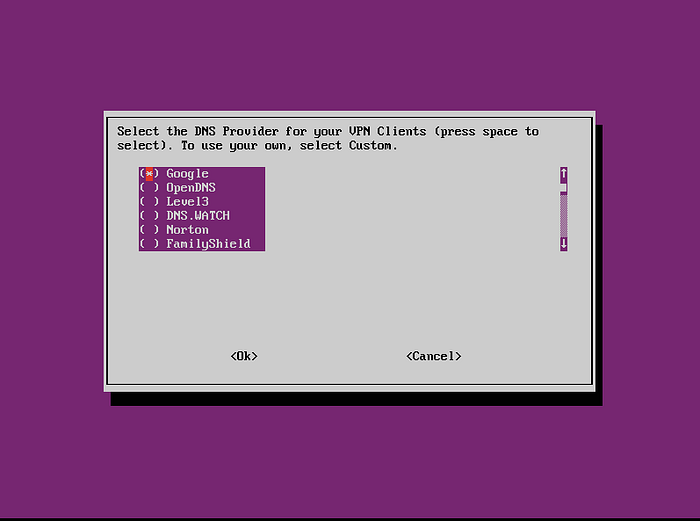
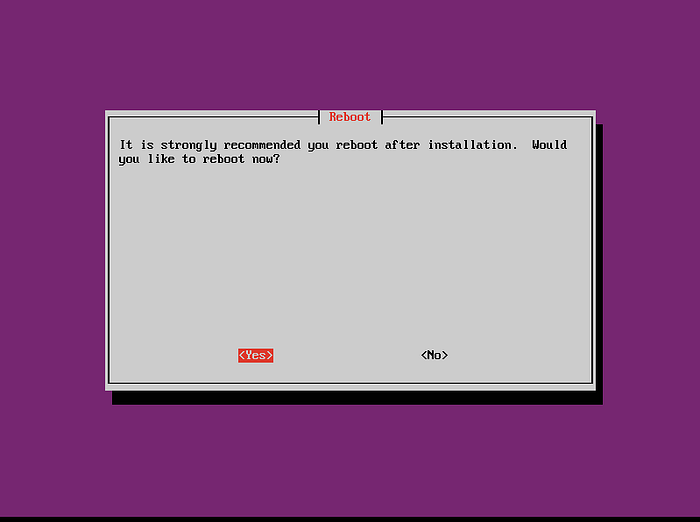
The installer will prompt you for various pieces of information as it moves from installation points. Initiall a local user should be chosen to hold the sudo permissions:



For the outside Internet to have access to the Router and then the PiVPN device, you’ll need to do some Port Forwarding on the Router. If you’re using a DynamicDNS service you’ll need to ensure you use the DynamicDNS domain and not a specific WAN IP address. I’d suggest using No-IP who offer 1 month free and then require re-validation each month. Log into your ISP router and access the `port forwarding` settings.
You’ll need to redirect all UDP traffic which enters to the port you decided on (e.g. 1194) to redirect to the IP and PORT of the Raspberry Pi at the PORT. Something like:
1194:IP_OF_PiVPN_MACHINE:1194
e.g. 1194:192.168.0.58:1194
* Remember that the PORT is what you set before and the IP you'll need can be found using the ifconfig command from the command line of the Raspberry Pi or Ubuntu machine you're installing on.
After port forwarding has been completed, you’ll need to generate login keys for your clients. They keys need to be transported in some way to the devices you’re using. Keys and details of login are generated in OVPN bundles. The OVPN file will have details on
These .ovpn files have all the settings and keys for clients to connect to the server. Create a new profile/keyset for each device you’re going to connect to the VPN. If I wanted to connect a PC:
linuxuser@mymachine:~$ pivpn
::: Control all PiVPN specific functions!
:::
::: Usage: pivpn
[option]
:::
::: Commands:
::: -a, add [nopass] Create a client ovpn profile, optional nopass
::: -c, clients List any connected clients to the server
::: -d, debug Start a debugging session if having trouble
::: -l, list List all valid and revoked certificates
::: -r, revoke Revoke a client ovpn profile
::: -h, help Show this help dialog
::: -u, uninstall Uninstall PiVPN from your system!
linuxuser@mymachine:~$ pivpn add nopass
Enter a Name for the Client: test_client_device
How many days should the certificate last? 1080
spawn ./easyrsa build-client-full test_client_device nopass
Note: using Easy-RSA configuration from: ./vars
Using SSL: openssl OpenSSL 1.1.1b 26 Feb 2019
Generating a RSA private key
………………+++++
…+++++
writing new private key to '/etc/openvpn/easy-rsa/pki/private/test_client_device.key.C2zG19qa0a'
Using configuration from /etc/openvpn/easy-rsa/pki/safessl-easyrsa.cnf
Check that the request matches the signature
Signature ok
The Subject's Distinguished Name is as follows
commonName :ASN.1 12:'test_client_device'
Certificate is to be certified until Aug 5 09:27:53 2022 GMT (1080 days)
Write out database with 1 new entries
Data Base Updated
Client's cert found: test_client_device.crt
Client's Private Key found: test_client_device.key
CA public Key found: ca.crt
tls-auth Private Key found: ta.key
========================================================
Done! test_client_device.ovpn successfully created!
test_client_device.ovpn was copied to:
/home/linuxuser/ovpns
for easy transfer. Please use this profile only on one
device and create additional profiles for other devices.
The key created for that device now needs to be transported to the device, where it may be used with an OpenVPN client or such-like support. Its recommended that you transport the key securely.
The next issue is connecting to the VPN with your OVPN key from you client device. OpenVPN Clients are recommended as they exist for a number of platforms like Android, PC, Mac etc. There is an OpenVPN Connect app for both iOS and Android. On Linux you can use the OpenVPN software. For Windows use the OpenVPN Desktop Clients. Further information is available on the OpenVPN site.
You should now be ready to go.

